SPRING-BASED CYBERSECURITY
for SCADA, PLC, and all other Industrial Control Systems in Process Plants & Manufacturing
The Problem
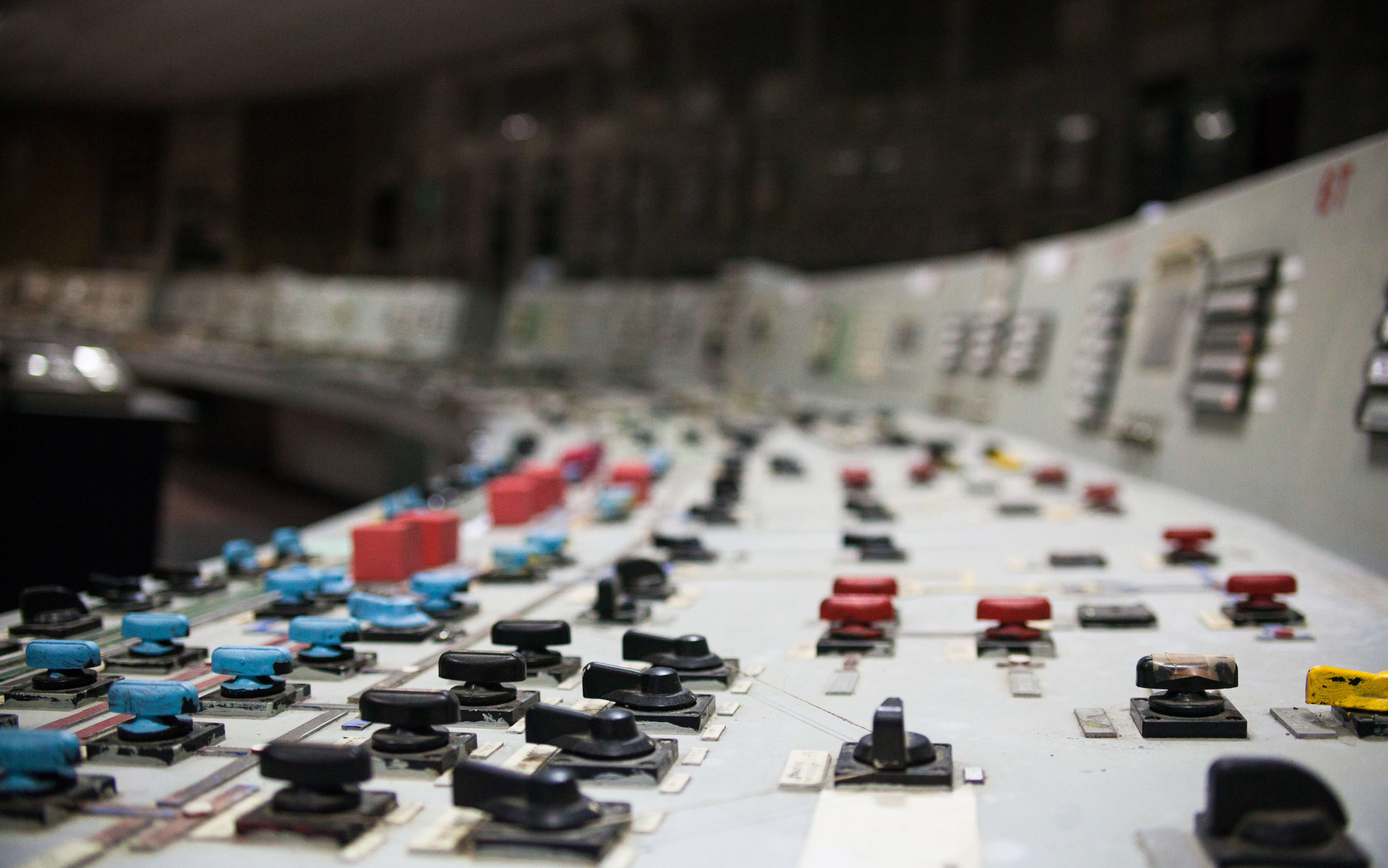
We have become very comfortable using advanced controller technology and in some cases, we are not thinking through the potential problems the technology might cause. Just this week, a news story Meanwhile, we are also building our processes and manufacturing plants with the same basic type of technology. How long before someone figures out how to hack the control process and destroy a machine or worse? Actually, that has already happened more than industry wants to admit. It may be happening to your facility right now and you just don’t know it. It might be masked like Stuxnet was, as best described in Ralph Langner’s paper “To Kill A Centrifuge”[2]. Consequently, the hack might appear as a nuisance problem, erratic or unreliable behavior. Much of the problem is coming from the advance of microprocessor and network communication technology and consequent implementation in programmable controllers and supervisory systems. This is excellent technology and its implementation has saved businesses a great deal of money from improvements in just-in-time, inventory-in-progress, as well as quality and more. Because of the benefits, I would be very hesitant to tell you not to integrate between processes or to avoid integrating the production processes with the business systems. You just need to do it very well. Recently, I heard about a convergence of control and safety that was being considered in the safety-instrumented-system market. As an ex-Navy submarine nuclear operator, I am not comfortable with the concept, even though I personally have advised engineers all over the world in the use of automation technology to solve the challenges they encounter. While there may be some economical benefit by combining systems, the costs to the business for the fix may put the business in a difficult financial position. Now is the time to exercise caution in automation technology that we use because it may not work correctly when we need it most. Facilities that process chemicals, or oil and gas, are regulated and monitored by government agencies like Occupational Safety & Health Administration (OSHA) Process Safety Management[3] and the UK’s Heath and Safety Executive[4] to insure that they are taking the necessary steps to protect against the very real consequences of a malfunction or abnormal state where the machine, people or the environment could be damaged. This practice is well established and documented in engineering standards including ANSI/ISA-84.00.01-2004 Parts 1-3 (IEC 61511 Mod), “Functional Safety: Safety Instrumented Systems for the Process Industry Sector,”[5] as well as the IEC 61508[6] standard. Additionally, process industries are systematically assessed to determine what hazards scenarios might occur that could result in a significant consequence, and for each of these scenarios, the safeguards that are available to prevent the accident are assessed to determine if they are adequate. This exercise is called a “Process Hazards Analysis”, and in the United States, it is required to be performed (and revalidated every five (5) years) for all facilities that pose a significant hazard by the labor regulator – the Occupational Safety and Health Administration (OSHA 3132)[7]. Jurisdictions outside of the United Sates have similar requirements. Process Hazards Analyses are performed using a variety of techniques. A common technique is the Hazards and Operability Study, or HAZOP. In a HAZOP study, a facility is broken down into “Nodes” of similar operating conditions and walked through a set of deviations, such as High Pressure, Low Temperature, Reverse Flow, etc. For each of these guidewords, a multidisciplinary team (e.g., operations, safety, and engineering) determines if there is a cause of that deviation beyond safe operating limits. If so, the team determines the consequence if the deviation were to occur, and then lists all of the safeguards that are available to prevent that deviation from occurring – or at least escalating to the point where damage can occur. During the PHA process (or HAZOP) by adding a Cyber-Check, each scenario is reviewed to determine if a pathway that is subject to exploitation via cyber-attack (i.e., “hackable”) exists. If so, the cyber-attack inherently-safeguard should be recommended. With respect to initiating events, or causes, in order to be hackable, the physical cause discussed in the HAZOP would have to be made possible through a command from the industrial control system. A review of all of the safeguards should be done next to determine if they are hackable. If the deviation in the HAZOP includes at least one non-hackable safeguard, then the deviation cannot be generated through a cyber-attack and is thus considered not hackable. If you get through the study and find that anything is hackable, you need to look at the consequences to determine if that deviation results in a significant consequence. If not, that attack vector is essentially a nuisance that is best left to traditional cyber-security. If the consequence is significant, then it is incumbent upon the analyst to make a recommendation to add a non-hackable safeguard. This is not required as frequently as one would think, and is not difficult to accomplish. The safeguard designer will always have the option to “mimic” one of the programmable electronic system safety instrumented functions with an analog pathway (i.e., generalized control loop current monitor relay). For instance, in the case of a high reactor temperature opening a depressuring valve as a safety instrumented function, if the control function is located in a safety PLC; then, in theory, it can be hacked. But, if an analog signal splitter on the 4-20 mA signal from the temperature transmitter, including a currently monitor relay, is utilized to interrupt power to the solenoid valve to the pneumatic circuit of the depressuring valve –an analog secondary pathway for that safety instrumented function that is hack-proof is thus created. By going through the PHA Cyber-Check process, plant designers can ensure that any process plant is inherently safe against cyber-attack. This type of safety does not rely, in any way, on the cyber-defenses that are employed at the facility, only the physical design of the plant itself. A number of safeguards are commonly employed in the process industries that are inherently safe against cyber-attack including the analog path described above. We are only going to talk about two other common devices, the mechanical over-speed and a pressure relief valve. These are basic safeguards based on a simple mechanical device, the spring. There are devices for both of these functions based on other technology, but this article is based on the spring. As the shaft of a rotating device increases in speed, the centrifugal force at the outer edge of the shaft increases. The centrifugal force on a weighted trip element extends the spring with which the element is attached to the shaft. Once the element extends beyond the safe limit of rotational speed, it physically strikes a switch arm which is mechanically linked to the valve that is supplying the medium causing the rotational force (e.g, a steam supply valve). The use of mechanical over speed trips on high-speed rotating equipment is very common, especially on older equipment. Only recently have designers opted to use programmable controllers for over-speed protection, leaving themselves vulnerable to cyber-attack. Meanwhile, it is reasonable to assume that an over-speed device along with an over-pressure device on the high-speed uranium centrifuges, could have prevented most of the physical damage caused by the STUXNET attack referred to earlier. Relief valves are ubiquitous in the process industries. In fact, in the United States use of relief valves is required by law for virtually all pressure vessels. The alleged cyber-attack where over-pressure damage was caused in the August 2008 Baku-Tbilisi-Ceyhan (BTC) oil pipeline explosion in Turkey [8] likely would have been prevented by this simple safeguard. Process industry plants contain hazards whose consequences can be very severe if a loss of containment were to occur. Process industry design engineers have a great deal of experience in protecting these facilities. Many of the safeguards that have been designed to protect process plants were developed years before computers even existed, and thus are inherently safe against cyber-attack if employed. We should not stop using them and should consider evaluating their use with the HAZOP Cyber-Check method more often, and in other types of manufacturing and process. [1] http://www.wired.com/2015/07/jeep-hack-chrysler-recalls-1-4m-vehicles-bug-fix/ [2] http://www.langner.com/en/wp-content/uploads/2013/11/To-kill-a-centrifuge.pdf [3] https://www.osha.gov/SLTC/processsafetymanagement/ [4] http://www.hse.gov.uk/enforce/index.htm [5] https://www.isa.org/store/products/product-detail/?productId=116704 [6] http://www.iec.ch/functionalsafety/ [7] https://www.osha.gov/Publications/osha3132.pdf [8] http://www.homelandsecuritynewswire.com/dr20141217-2008-turkish-oil-pipeline-explosion-may-have-been-stuxnet-precursorFunctional Safety Background
Identifying Where Inherent Safety Against Cyber-Attack is Required
Spring Based Cyber Secure Device Examples
 Mechanical over-speed trip devices that are present on turbine control systems, or any other piece of high speed rotating equipment, use various technologies including a simple mechanical spring to prevent the machine from damaging itself from running to fast. These typically dump steam or whatever the prime mover is so that the rotating machinery can slow down. I included a simple drawing of a mechanical over-speed switch for reference.
Mechanical over-speed trip devices that are present on turbine control systems, or any other piece of high speed rotating equipment, use various technologies including a simple mechanical spring to prevent the machine from damaging itself from running to fast. These typically dump steam or whatever the prime mover is so that the rotating machinery can slow down. I included a simple drawing of a mechanical over-speed switch for reference. A pressure relief valve protects pressurized piping systems and vessels from bursting or otherwise leaking as the result of pressure in the equipment becoming higher than the equipment can withstand. The relief valve is mounted so that the inlet nozzle is directly connected to the protected process, shown as the arrow pointing into the valve in the drawing provided. As the pressure in the process increases beyond desirable limit, the force of pressure in the vessel overcomes the pressure of the spring, safely venting the vessel’s contents to a containment or disposal system and preventing damage to the process equipment.
A pressure relief valve protects pressurized piping systems and vessels from bursting or otherwise leaking as the result of pressure in the equipment becoming higher than the equipment can withstand. The relief valve is mounted so that the inlet nozzle is directly connected to the protected process, shown as the arrow pointing into the valve in the drawing provided. As the pressure in the process increases beyond desirable limit, the force of pressure in the vessel overcomes the pressure of the spring, safely venting the vessel’s contents to a containment or disposal system and preventing damage to the process equipment.Conclusions